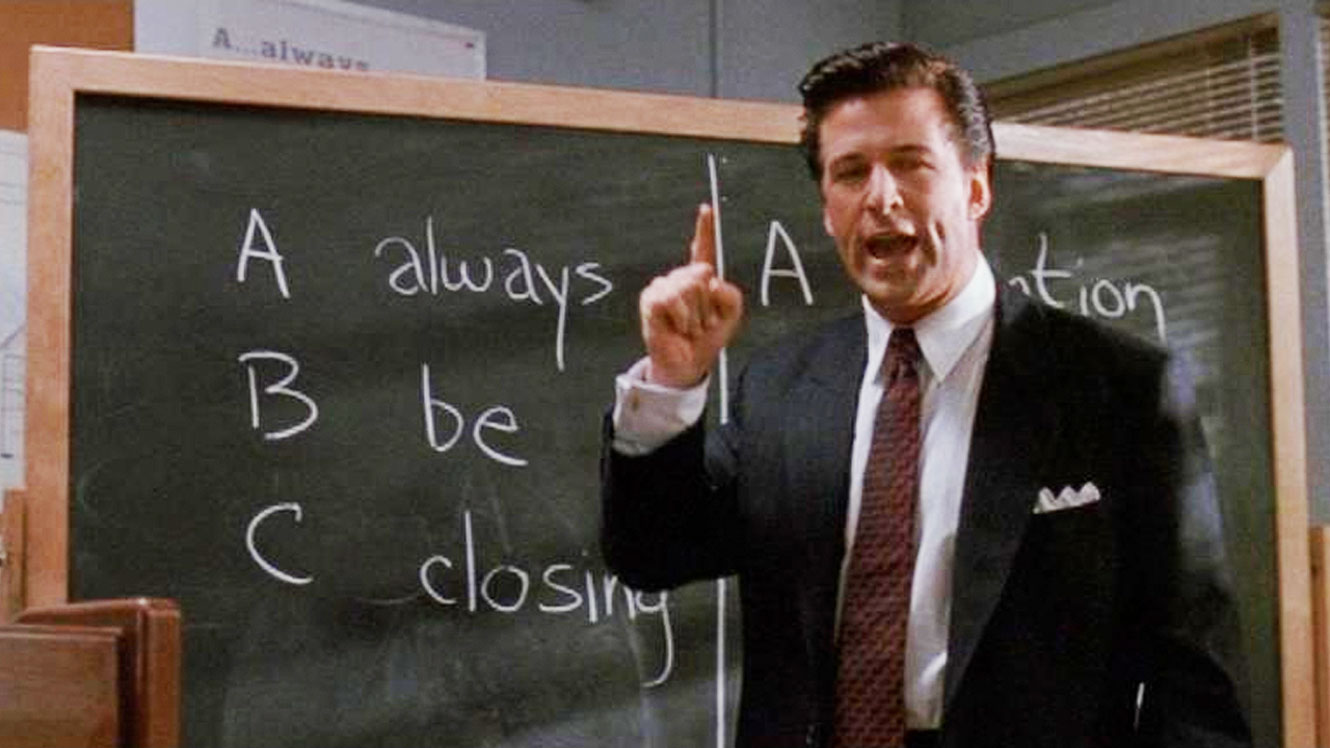
“These are the new leads. These are the Glengarry leads. And to you they’re gold, and you don’t get them. Why? Because to give them to you is just throwing them away. They’re for closers.†–Glengarry Glen Ross
This past week I got around 70 cold calls or emails from vendors I’ve never worked with wanting to see if they could schedule a 15-20 minutes with me. I’ve had the usual responses to this. At some point, I stopped answering my phone if I don’t recognize a phone number. But recently this has gotten me to thinking that salespeople act a lot like hackers. They use the same social engineering techniques that hackers use, and when they’re good at their jobs they can do it better. It’s a cool way of thinking about being a salesperson…if you’re a salesperson.
Unfortunately, salespeople in the cybersecurity field can’t act like hackers. The problem is that the security community expects them to be knowledgeable with security, and when they use social engineering techniques, that will be setting off alarm bells in their potential customers minds. It makes me question whether the person selling security really understands what they’re selling.
Since I can’t tell the difference between a real salesperson and a hacker impersonating a salesperson, my default is to run with the assumption that you’re a hacker until I believe otherwise. Unfortunately, many vendors work really hard to prove me right.
“Put that coffee down. Coffee is for closers.â€
Here are some common mistakes security salespeople make, and why these approaches are problematic:
- One of the questions I most frequently receive is, “can you tell me who at your company is responsible for x, y, and z.†You can probably get a very good idea of this through LinkedIn, so why would you ask this? If you were a social engineer, you’re building a profile of my organization and you want to get a warm introduction to the target of the attack, so you don’t start with the target. You start with someone with authority who can provide you a handoff while avoiding raising any red flags.
- Another common type of reconnaissance question is, “What kind of firewalls do you use?†If you were a hacker, and I’m assuming you are, this is helping you to profile my network for a future attack, or further refine a penetration already in progress.
- Another common social engineering technique is to build authority, and many vendors do this by name-dropping their customers. This isn’t a huge problem, and if I see this in a powerpoint, I’ll assume that you’ve gotten permission from those customers to use their names. But if you’re using this just in passing or to keep me on the phone, it looks like you won’t keep your customer’s information confidential. If I want a reference customer, I’ll generally ask for one.
- You are not my account manager if I don’t have an account with your company. This is the most frequent ways that salespeople will introduce themselves. While it may be true that your company will dedicate you to serve me if I agree, I haven’t agreed to this arrangement yet. I think this is another way of establishing authority. Similarly, don’t tell me you’re calling because I downloaded a whitepaper when I haven’t.
- My favorite is the guilt trip email. After doing several cold calls and maybe a few email follow ups, they’ll say, “George, did we do something wrong? This will be our third and final email.†If you’ve gone through any phishing training, no doubt you’ve seen that a common red flag is setting an artificial deadline to create urgency. With urgency comes emotion, and that emotion can cloud the judgment we need to avoid the trap. This feels the same to me. And it’s just a lame thing to say to someone.
Okay, that sounds harsh.
I get that vendors need to sell products. I’ve also been delighted when I discover a new product that we desperately need. We need great partners who can bring those products to us. I focused one of the chapters in my book, No More Magic Wands, on how having great partners can open you up to work on the big picture of security for your company.
I’m not a salesperson, but I do have some advice to help me to believe you’re a regular person and not a hacker:
- Help build relationships. Some of my best partners started out by getting to know me and introduced me to other people in the profession. I’m pretty sure you’re not a hacker if I meet you in real life and a lot of other people seem to know you.
- Build business cases for your products. If I truly do want to move forward with your product, I will need to do a justification and this just helps me get there faster. Maybe you can get another customer to share this or maybe you can build one yourself. It shows you’re thinking about what I need and to build a long term partnership, and not trying to do some recon.
- Give back to the community. Last year, I volunteered to help the Security Advisor Alliance with one of their virtual capture the flag events at a local high school. There were a number of vendors who also volunteered to help and I’ve gotten to know some of them after the event.
Partnership is a two way street. For my part, once I’ve built a relationship with a vendor, I give back to that relationship. In the past, I’ve done case studies or speaking engagements about my experiences with a vendor. I’ve been a reference account and talked to prospective customers about my experiences with a vendor. I’ve hosted user group meetings at my site so other customers can come together and we can all share our knowledge and use those products better. I actually gave a vendor tickets to one of my University’s football game once as a thank you for saving my bacon.
Maybe I’m one of those bad leads, but I think being a partner and a hacker are mutually exclusive.