Bullet Resistant Cybersecurity Advice

In the beginning of Andrew Carnegie’s famous book, How to Win Friends and Influence People, he tells the story of safety inspector George Johnston. Johnston’s job was to get people to wear hard hats at construction sites. He would tell them, with the force of his authority, that they should wear their hats — even […]
The Top 10 Best Cybersecurity Strategies

After reading the great list of the Top 10 Worst Cybersecurity Strategies from Matthew Rosenquist I started thinking about what a similar list might look like for best cybersecurity strategies. We often focus on what not to do in cyber…and this makes sense, it’s more efficient to avoid problems. Where is the advice on what […]
The 60 Questions To Ask Before You MSSP Your SOC

Next week, I’ll be giving a talk “To MSSP or Not to MSSP: Some SOC Questions†at Educause Security Professionals. I’ve never met anyone who has said they love their MSSP. My team and I have been through several POCs with MSSPs, and have used several SOCs with various results. I don’t think there is […]
Culture Eats Cybersecurity For Breakfast

Eggo Waffles weren’t always called Eggo Waffles. In the 1950s, in the boom that followed World War II, Americans began a love affair with frozen foods. Frank Dorsa and his three brothers in San Jose California had been running a highly popular mayonnaise business and had expanded into powdered waffle mix, but demand for their […]
Unsolicited Advice For Solicitors: Part Deux – An Unexpected Calendar Entry

I got a calendar invite from a vendor this week. Several of my colleagues were included, but not ones that I would normally meet with. I had never met this vendor before. I had never exchanged emails with this salesperson. I checked with my colleagues and none of them had ever had a conversation with this individual either. As I […]
What Toys R Us Taught Me About Growing Up
When I was in high school, I got a job working at Toys R Us. It was one of the best jobs I ever had, and to this day I still think about all of the lessons I learned about service to others, responsibility, and integrity. My secret ambition was to be able to wear […]
The Funny Thing About Blind Spots

When I was in college, I got a job one summer at a comedy club. It wasn’t as glamorous as it sounds. I didn’t get to meet any comedians. My job was essentially a telemarketer. I would call people who had attended previous shows and tell them they had won free tickets to see the […]
The Best Job I Ever Had

“Security is mostly a superstition. It does not exist in nature, nor do the children of men as a whole experience it. Avoiding danger is no safer in the long run than outright exposure. Life is either a daring adventure, or nothing.†-Hellen Keller In honor of Labor Day, I’ve been reflecting on my career […]
Cybersecurity New Years Resolution
I don’t normally make New Year’s resolutions. But when I do, I start them in March. As you may have noticed, I decided to start blogging again. I published a book last year on cybersecurity for the layperson (managers, salespeople, executives) and I knew I wanted to begin writing a sequel. I didn’t have a theme […]
Cybersecurity Training Scars

There’s an old story in law enforcement circles that comes from the era of revolvers. During practice, officers would dump their spent brass cartridges into their hand after shooting a round rather than letting the brass fall to the floor where other people might slip and fall on it. Officers would then take the time to put […]
An OSI Model for Security Awareness

There are two parts of every great performance: the outer game and the inner game. Most books on coaching focus on the outer game. The outer game is what happens on the field. What sport are you playing? What plays are happening? What techniques are you using to hold or hit the ball? How do […]
It’s Always Sunny In Cybersecurity
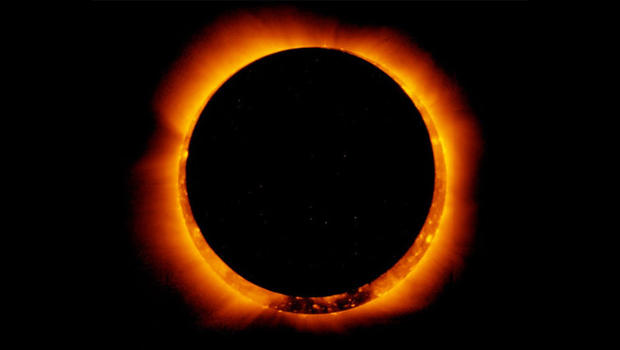
In ancient times when there was a total eclipse, many people believed that evil was taking over the world. In those days, before telescopes or astronomy, people believed that the sun was some sort of god: the Greeks called this god Helios and the Egyptians called him Amun-Ra. The idea that a god could be […]
Cybersecurity Secret Santa

One year, I asked for a video game for Christmas. This was back when video games still had cartridges and came in a very distinctive package. So when I saw this familiar shape with some Santa Claus wrapping paper around it, I knew I had gotten what I wanted. I usually had two hours after […]
Abundant Cybersecurity

I was talking with a fellow CISO at a conference recently and she said something that resonated with me. She had just acknowledged that she wasn’t fully staffed and that her budget was down slightly. “But we’re doing better than we ever have,†she explained. It took a few weeks for me to process this, […]
The Nine Habits of Highly Effective Cybersecurity People

I was interviewing a manager recently about his department’s cybersecurity practices when I asked him whether they lock their paper records up at night. He said yes, they keep their files locked at all times, not just at night. I pointed to the filing cabinet in his office, where they key was still sticking out […]
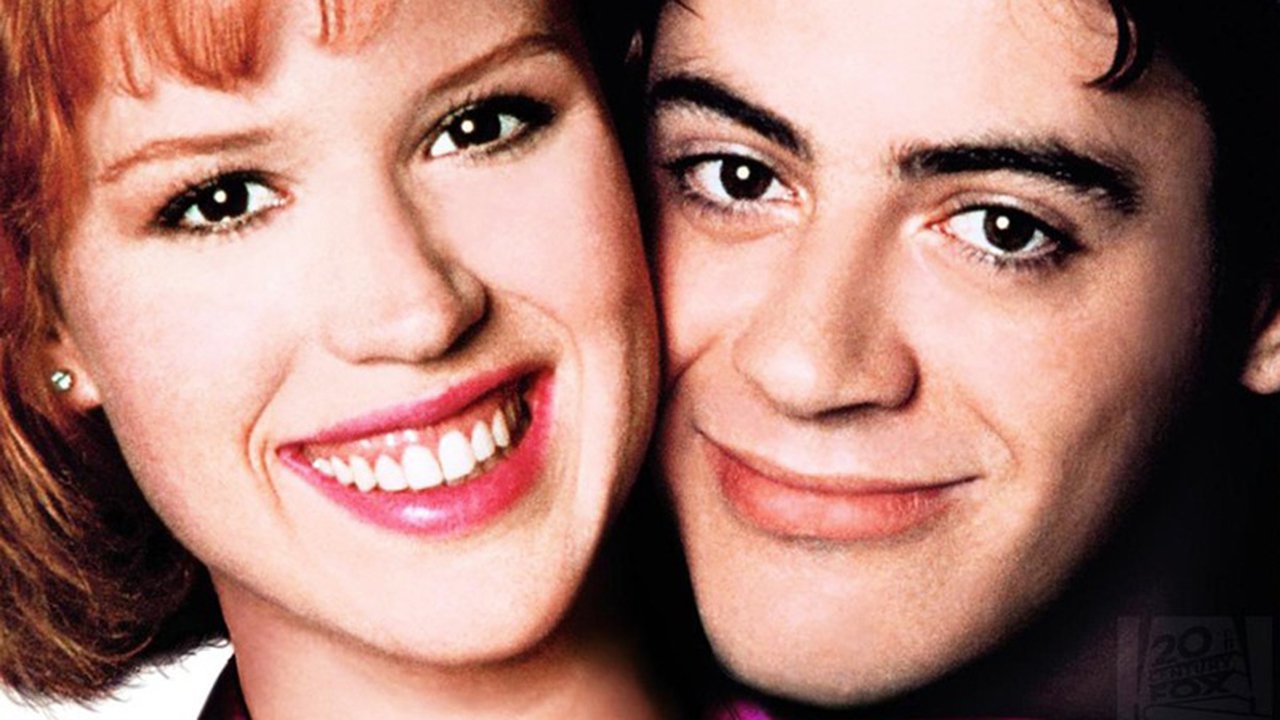
Cybersecurity Role Models

Every time I interview a candidate, I ask, “Who is your role model in cybersecurity?†Some candidates name famous hackers, like Kevin Mitnick. Others choose well-known journalists like Brian Krebs or a prolific writers like Bruce Schnier. One candidate said their role model was Neo from the Matrix movies. There isn’t any right answer to this […]
You’re Fired – Cybersecurity Apprentice

You’re fired. No, this isn’t about a politician’s catchphrase. It’s actually something I overheard at a conference last year. I was listening to two people sitting near me talk about a security incident that had happened at the woman’s company. “He should be fired,†was the other person’s immediate response. This makes me wonder if […]
Security Awareness Training, Now With Personality!

I had the opportunity a couple of months ago to meet Kevin Finke at a conference. Kevin isn’t a security guy, he’s a self described design nerd. But Kevin has changed the way I look at my security awareness program. We talk a lot about how we need to “revolutionize†our security awareness programs, but […]
The Next Generation of Security Professionals

Yes…that’s me and my wife, hanging out with Jeordi LaForge (LeVar Burton), Dr. Beverly Crusher (Gates McFadden), and Mr. Data (Brent Spiner). Trek yourself before you wreck yourself. In The War of Art, Steven Pressfield says that the difference between an amateur and a professional is that the professional has a plan. According to CSO […]
Unsolicited Advice For Solicitors
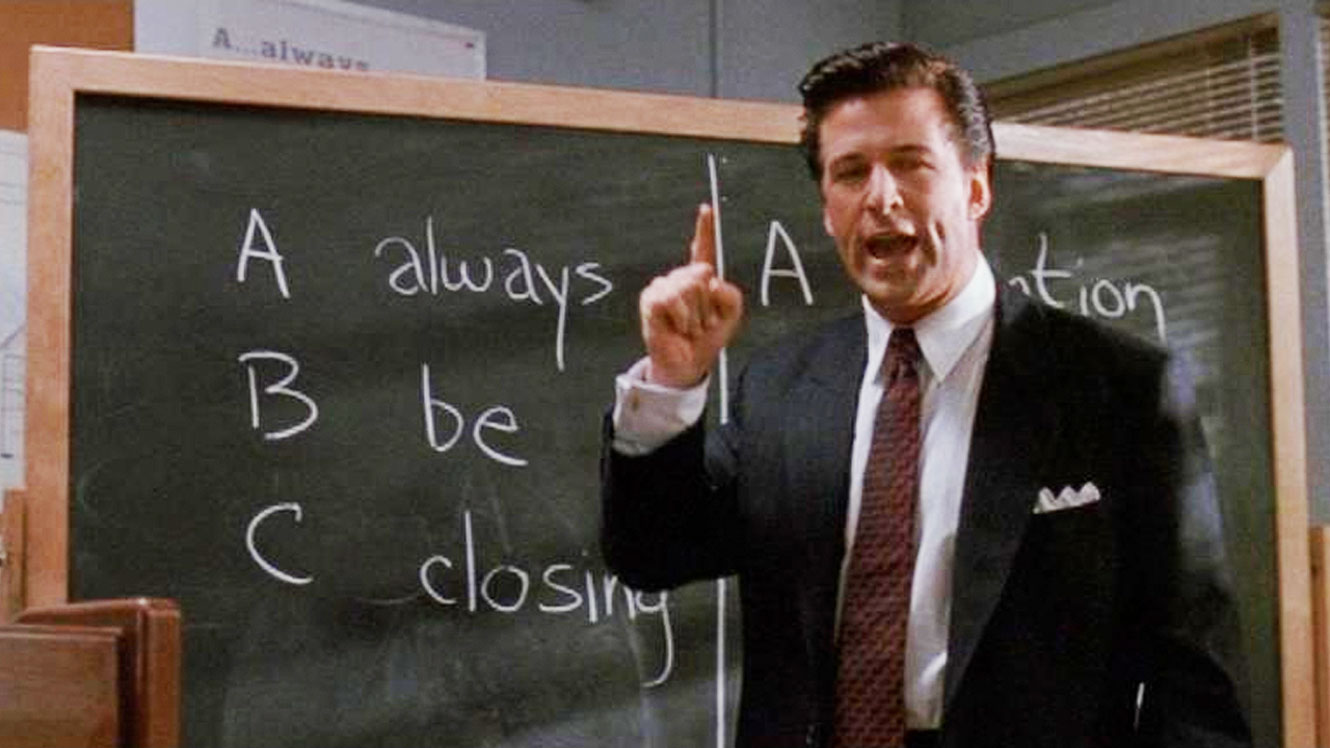
“These are the new leads. These are the Glengarry leads. And to you they’re gold, and you don’t get them. Why? Because to give them to you is just throwing them away. They’re for closers.†–Glengarry Glen Ross This past week I got around 70 cold calls or emails from vendors I’ve never worked with […]
Pick Up Lines Vs. Social Engineering
One of my favorite pickup lines goes like this…have a girl feel the cuff of your jacket or shirt. Ask her, “do you know what kind of material this is”? And when she says no, tell her “boyfriend” material. Here’s a thought exercise. (Disclaimer, I could be totally wrong. Also, I’ve never used a pick […]
Herd Immunity & Information Sharing In Cybersecurity

As I raise my child, I’m continually amazed at how fragile we are as a species. What’s more, how do animals survive in the wild? Not only do herds of giraffe’s or antelope have to face illnesses, they have to fight off large predators. We’re in a similar situation with cybersecurity. Hackers act in a […]
Show Me the Money: Incentivizing Cybersecurity

What I’m about to tell you, it’s a very personal, a very important thing. Hell, it’s a family motto. Are you ready? Here it is: Show me the money. SHOW! ME! THE! MONEY! A core principle of nearly every business in the world is that they incentivize great performance. This might be a monetary bonus […]
Cybersecurity’s Happy Gilmore Problem
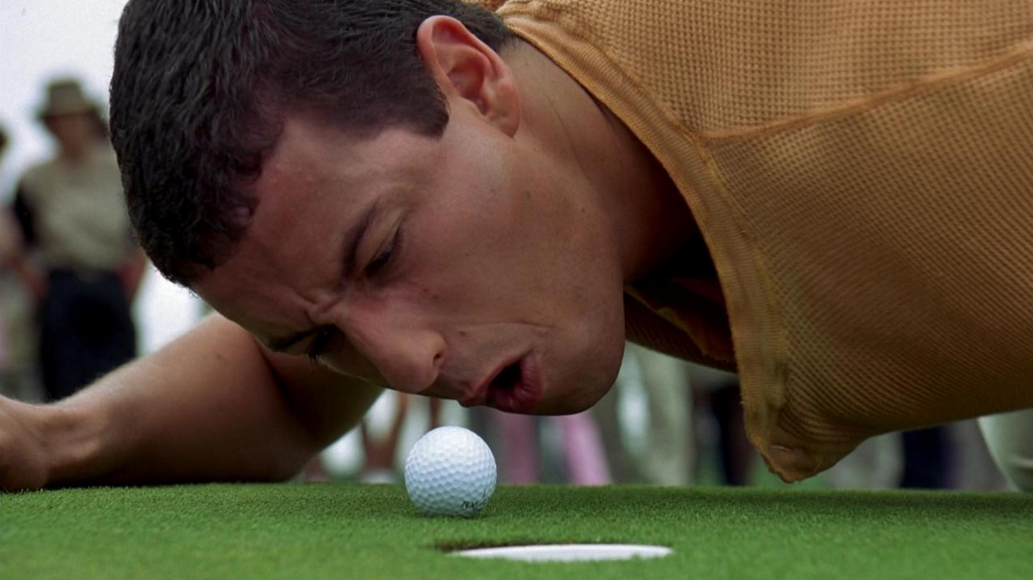
People, processes, and technology are the three parts of every security program. Sometimes, people make the mistake of believing that technology is the biggest or most important part. It isn’t. It might be the easiest part, since you can make quick changes to technology and buy new things to instantly improve it. But the biggest […]
Between The Keyboard And The Chair

I have a lot of respect for people who work at a help desk. When I was right out of college, I got a job at a call center. I had to take an average of one call every 4 minutes. That means I talked to 120 people every day on average, and a lot […]
The Strongest Element

In Cybersecurity we refer to employees as the Human Element. We generally call the Human Element the weakest link in Cybersecurity. It’s easy to see the logic in this, but unfortunately for many of us, this is wrong. Humans are the Strongest Element in Cybersecurity. Sure, humans are the ones that make the mistakes. They […]
Embracing Wellness in CyberSecurity

CyberSecurity is a life skill.
Extending CALEA to Cover the Cloud?
There is a great discussion over on Slate about how the FBI sees it’s ability to listen in via tapping phones as “going dark”. Why use a landline or a cell phone when you can use your webcam to orchestrate your criminal enterprises? http://www.slate.com/blogs/future_tense/2013/03/26/andrew_weissmann_fbi_wants_real_time_gmail_dropbox_spying_power.html The blog suggests that the FBI is interested in extending CALEA, […]
Judicial Revolt Against Invasions of Privacy
Last week saw two major Judicial decisions related to privacy come out of the 9th Circuit, perhaps signaling a new offensive against warrantless wiretapping. First, a Federal Appeals court ruled that customs agents no longer have carte blanche to search electronic devices coming into the country. The 9th Circuit decision has an impact on border […]
Privacy, Customs, and You
If you are travelling to Mexico and you are a technophile, good news! The 9th Circuit now says that Customs agents no longer have carte blanche to search your devices. See more from the Wired article: http://www.wired.com/threatlevel/2013/03/gadget-border-searches/ The 9th Circuit decision has an impact on border crossings into California and Arizona. That doesn’t mean that […]
Was Aaron Swartz the victim of Prosecutorial Overreach?
After Aaron Swartz’s tragic death in 2012, a lot of bloggers have started throwing around the term, Prosecutorial Overreach when talking about Federal prosecutors Carmen Ortiz or Stephen Heymann. The problem is that this is a new term, invented seemingly out of nowhere in 2012. It sounds like legalese, but it isn’t a Legal term. […]
Pentagon to use Nukes against Hackers?
What’s the latest weapon in the Cyber Arms race? Nuclear bombs, apparently. http://www.acq.osd.mil/dsb/reports/ResilientMilitarySystems.CyberThreat.pdf Okay, let’s not over react. The report says that the U.S. would only use nukes under extreme circumstances. Hopefully that doesn’t mean viagra related SPAM. Seems like, if anything, maybe an EMP would be a better alternative?
Privacy is Dead: Now Where’s My Inheritance – Part 3
As an American, when I picture the beginnings of civilization, I don’t picture Neanderthals huddling together in caves. I picture the pilgrims landing on foreign soil, building log cabins to sustain themselves against the winter. With the hope of a new frontier to explore. It strikes me that we are in the same position when […]
Diplomatic Immunity
The White House this week released a plan to stop state sponsored hacking, like the one uncovered by Mandiant this week, through the use of diplomatic pressure. The 72 page report details the measures that the White House is willing to use as leverage. The strategy stops short of threatening economic or other types of […]
Privacy is Dead: Now Where’s My Inheritance – Part 2
In Part 1 of my Post, Privacy is Dead, I estimated that giving up Privacy in exchange for a number of benefits could be worth as much as $10,000 per year to an individual. While this isn’t pocket change for most of us, for someone making minimum wage, this might represent 6 months of work. […]
Privacy is Dead: Now where’s my Inheritance – Part 1
Privacy is Dead. It’s not the first time you’ve heard this, surely. A private investigator, Sam Rambam was quoted as saying “Privacy is Dead – Get Over it†in 2006. In 2012, Huffing Post contributor Miles Feldman posed the question “Is Privacy Dead?†If it is, then we’ve been collecting our inheritance without knowing it […]
Instagram Apocalypse 2013
Everyone knows that the Mayans may or may not have predicted that the world will end on December 21, 2012. Experts are now saying that there is another major calamity awaiting right around the corner for those of us who survive on January 16, 2013. That’s when Instagram’s new privacy policy will take effect. There […]
Safe Web Act Reauthorized
Some laws are permanently on the books. Other laws have a sunset date…like the Bush Era Tax cuts. Sunsets have become popular these days as a way of keeping Congress honest so they have to renew the laws if they think they worked out well. The Safe Web Act was one of those laws. Safe […]
Warrantless Wiretap-Dancing
Yesterday the Senate Judiciary Committee voted to update a law, the Electronic Communications Privacy Act, (ECPA), to require law enforcement to obtain a warrant before conducting searches of people’s online communications, including email, Facebook posts, Twitter updates, and documents stored online. The full Senate is not expected to vote on the changes to the law […]
Controversial Cybersecurity Act Vote Coming Soon?
This week, House Majority Leader Harry Reid hopes to finally bring the long awaited Cybersecurity Act of 2012 to the floor for debate. Senator Joe Lieberman and the four co-sponsors of the Cybersecurity Act introduced a revised version last week, which they indicate incorporates extensive negotiations with the bill’s opponents. The Hill’s Technology Blog reports […]
What happens when a public company has your private data?
What happens when a public company has your private data? It used to be that Facebook was owned and operated by a private citizen. Sure it was fun to question his motives. Those were the days. Maybe it wouldn’t have changed if Facebook shares had started to skyrocket from the getgo, but they didn’t. And […]
Obama ordered Stuxnet
According to an upcoming book by New York Times chief Washington correspondent, David Sanger, it was Obama who ordered the Stuxnet attack against Iran’s nuclear program. This isn’t really a surprise, since most people believed the US to be behind the attack, but it does continue Obama’s M.O. of preferring special forces over direct and […]
On tbe Front Line of the Cyberwar
Interesting article on NPR about whether businesses should foot the bill for a Cyber War. The Lieberman-Collins bill before congress would help pay to secure the nation’s critical infrastructure like the power grid, water treatment plants, and the financial system. Does the government have a duty to protect the rest of the country? I think […]
Facebook "Likes" Not Protected Speech?
ArsTechnica has a great summary of the case of Bland v. Roberts, which has ruled that Facebook “Likes” are not protected speech under the 1st Amendment. The case was decided in the Eastern District Court of Virginia, so it could be appealed a couple of times before hitting the Supreme Court… There have been lots […]
CISPA Defections Begin
An update on my last post, CISPA – The Government’s consolation prize for not passing SOPA, it looks like the measure has already lost some of its original supporters. According to a story on TheHill.com, seven of the original cosponsors of the Cyber Information Sharing and Protection Act (CISPA) abandoned ship and voted “No” on […]
CISPA – The Government’s consolation prize for not passing SOPA
Yesterday, the U.S. House of Representatives passed the Cyber Intelligence Sharing and Protection Act (CISPA). While the bill was introduced with bibartisan sponsors, the bill passed the house on mostly party lines…Republican “yes” votes were 206 and Democrat “No” votes were 140. Both sponsors were the ranking members of the House Intelligence Committee. 42 democrats […]
America losing the Cybersecurity war?
Interesting blog post on Computerworld today: http://blogs.computerworld.com/19951/cybersecurity_america_is_losing_the_war_china_hacked_every_major_us_company?source=CTWNLE_nlt_pm_2012-03-28 Lots of doom and gloom.
McCain vs. Lieberman – SecureIT vs. Cybersecurity Act of 2012
Senator John McCain along with 5 other Republican senators released their counterproposal to the Lieberman-Collins Cybersecurity Act of 2012 released last month. The bill is called the Strengthening and Enhancing Cybersecurity by Using Research, Education, Information and Technology (Secure IT) Act. Let me start by saying that when I see a bill that cleverly named […]
Obama proposes Privacy Bill of Rights
Today, the White House released it’s proposal for a Privacy Bill of Rights. The press release is entitled “We Can’t Wait“. Sound familiar? It’s because John Kerry and John McCain proposed this last summer. Obama’s proposal goes much further in terms of scope. The proposal includes several key principles: 1. Individual Control: Consumers have a […]
McCain Disses the Department of Homeland Security, Dashes Hopes for Security Bill in 2012
Senator John McCain last week dissed the Department of Homeland Security, stating that the NSA is better suited to preventing cyberattacks. Wait, what? The NSA has tremendous cyber capabilities, don’t get me wrong. But wasn’t DHS formed to prevent the kinds of bureaucratic nightmares of sharing information between agencies. The DHS has a National Cybersecurity […]
EU updates privacy policy
Yesterday, Google announced a major overhaul of it’s privacy policy to some loud criticism. It’s nice to see today that the EU has come out with its own updates to its privacy policy. Let’s compare the new EU data privacy rules to the US ones being proposed throughout 2011 in both the House and the […]
5th Amendment = Encryption?
A woman accused of bank fraud hopes to prevent the contents of her hard drive from being searched with encyrption. http://technolog.msnbc.msn.com/_news/2012/01/23/10219384-judge-orders-woman-to-give-up-password-to-hard-drive If this were the case, it would quickly become impossible for the criminal justice system to prove a lot of their cases. Interesting theory. The 5th amendment says: No person shall be held to […]
Shrinking Public Domain
The Public Domain got a little bit smaller this week: http://arstechnica.com/tech-policy/news/2012/01/supreme-court-rules-congress-can-re-copyright-public-domain-works.ars Perhaps the Supreme Court felt compelled to do something for copyright holders after the setbacks to SOPA and PIPA yesterday?
Should There Be a Cyberwar Treaty, Part 2
In my previous article on whether there should be a cyberwar treaty, I argued that Cyberwar wasn’t like other types of conflict, and that it wasn’t likely that a treaty would ever happen.Being a lawyer, I like to play devil’s advocate, so here’s a different perspective. Jeffrey Carr, in his new edition of “Inside Cyber […]
Say goodbye to the Video Privacy Protection Act
If someone posted a video of me having sex on the internet, which admittedly wouldn’t be very popular, I would sue them. Most likely I wouldn’t become very rich and very famous. Not like Paris Hilton or Kim Kardashian. Lawsuits for violations of privacy like this have made millions. Privacy lawsuits aren’t just limited to […]
Of RootKits and Cell Phones
Lawyers, this article is for you: Beware…using your cell phone for confidential conversations my violate client confidentiality! Why you ask? Because a 3rd party may be listening in on your 1) voice calls, 3) text messages, and 3) client emails. The company is Carrier IQ, and they have partnerships with every major cell phone carrier […]
Computer Fraud and Abuse Act (CCFA)
If I was an attorney (I am) and if I worked for an ISP (I kinda do), and I was feeling a little punchy…what if I decided to write into my terms of service for my organization that any user going to Google was a violation of their terms of service and their Internet access […]
Economic Espionage vs. Innovation
For the first time, the United States has publicly announced that it believes China is the world’s leading source of economic espionage. Robert Bryant, U.S. National Counterintelligence Executive, released the report Wednesday, essentially confirming what many government officials have been saying privately for years. The silver medal goes to Russia, who, in the words of […]
Why don’t Americans care about Privacy?
In my post from earlier this year, I commented on how Senator Leahy re-introduced his Personal Data Privacy Act…the same bill he has been submitted every year for the last 5 years. 5 months after the re-introduction of the bill this year, there is still no GOP support for Leahy’s Privacy bill. By my count […]
Crimesourcing
Imagine a world where criminals used sophisticated networks of middlemen. Transactions between pawns were untraceable. All using the power of something called, the Internet. And people wonder why I say that the law is having a hard time keeping up with technology. The article gives a great overview of the developments in cybercrime over the […]
Daubert’s Fingerprint
Everybody knows that every snowflake is one of a kind. Unique. Just like a fingerprint. Wait, how do we know a fingerprint is unique? In a legal proceeding in the United States, the process the court uses to determine whether an expert witness is qualified to give testimony in their field is commonly referred to […]
Cyberattack on Predator Drones?
Wired’s Danger Room points out that US Predator and Reaper drones have been under attack by a computer virus: http://www.wired.com/dangerroom/2011/10/virus-hits-drone-fleet To date, the virus has only apparently been logging the keystrokes of the operators. From the article, I get the impression that it is the operators workstations and not the drones themselves that are the […]
Netflix Hates Privacy?
There’s been a lot of news about how Netflix wants to fight an arcane video law, passed almost 25 years ago, to enable the future of movie streaming. Hulu wants to do the same thing, with their new video campaign, “This is my favorite part…†I like the Hulu commercials, but I’m not convinced that […]
Hacking is free speech!
Hacking Is Free Speech! (or is it?) I should start by noting that not all speech is protected under the 1st Amendment. For example, I can’t say to someone that I am a detective with Miami Metro Homicide, because I’m not. That’s called impersonating a police officer and carries a prison sentence. There are particular […]
What Would Jesus Hack
Interesting article in the Economist about the connection between Christian values and the values of the Hacker/Open Source Community: http://www.economist.com/node/21527031
The Privacy Bill of Rights
When it comes to the Federalist debates, I was always on the side that argued that creating a bill of rights would limit our rights rather than protect them. But, since we don’t live in that world, Congress is working on creating additional bills of rights (maybe this is just a fad). There was the […]
Porn Pirates vs. Copyright Trolls
We’ve spent the last 10 years hearing about the evil forces of the RIAA suing single mothers and grandparents without a computer. The entertainment industry has seen declining CD sales for a number of years. Whether this is attributable to piracy and programs like Napster is hotly debated. Behind the scenes, the RIAA has done […]
How Many DMCA Notices does the RIAA send every year?
How Many DMCA Notices does the RIAA send every year? This is a question I’ve been asking myself (and others) for years now. The solution was pretty obvious…on the tip of my proverbial nose the whole time. The RIAA appears to use a sequential numbering system in its case tracking system. There is no way […]
Should There Be a CyberWar Treaty?, Part 1
The Department of Defense released their Strategy For Operating In Cyberspace in July. In the document, they add Cyber to the traditional 4 domains…Land, Sea, Air, and Space. This paper raises the question, at least in my mind: Should there be a Cyberwarfare treaty? I think the short answer is a definite “Maybe.†I think […]
Cyberwar – Cyber Arms Dealers
Business Week has a nice article on the Cyberwarfront arms race: http://www.businessweek.com/printer/magazine/cyber-weapons-the-new-arms-race-07212011.html I think the most interesting part about the article is the idea of a Cyber “Arms Dealer”. This makes me wonder what other analogs to traditional warfare might be out there… Mercenary Hackers?
Hacker Hackett sentenced to 10 years
Good article at SecurityWeek on the case of a professional identity thief sentenced to 10 years in prison: http://www.securityweek.com/hacker-caught-675k-stolen-credit-cards-gets-maximum-prison-sentence The best part is his name: Hackett. Phonetically, that would be pronounced “Hack – It”. 10 years and a $100,000 fine for having 675,000 stolen credit card numbers which investigators believe led to more than $36 […]
Barack Obama’s Audacity of Hack, Chapter One
In May, the White House released a comprehensive proposal for a number of CyberSecurity measures. Unlike most of the other legislation proposed that focuses on Data Breaches or Do-Not Track. The White House proposal has 6 different sections that include changes to Homeland Security CyberSecurity as well as coordination of CyberSecurity between agencies. Data Breach […]
HIPAA Hot Potato – Federal vs. State
In May, The Office of the Inspector General issued a report on the results of an audit conducted for the Office of Civil Rights on the effectiveness of HIPAA compliance. The report wasn’t so great. “Although OCR stated that it maintains a process for initiating covered entity compliance reviews in the absence of complaints, it […]
Discussion Draft of the SAFE Data Act introduced by Representative Mary Bono Mack (R-CA)
On June 13th, Congresswoman Mary Bono Mack released a discussion draft of what she calls the SAFE Data Act. Here’s the marketing release if you’d prefer to read the cliff notes. Since it’s a discussion draft, let’s discuss! Actually, I think this could be a good bill to eliminate a lot of the confusion about […]
What has Al Franken done for me lately, Part 2
Last week, the Senate Committee on Commerce, Science and Transportation held a hearing on Privacy and Information Security. Senator Rockefeller made a point of emphasizing his committee’s jurisdiction over privacy and data security issues. I think this statement alone shows a rift in the Senate’s perspective on Information Security in light of the newly formed […]
War Powers Resolution and Cyberwar
If you’ve been following the war in Libya and the Obama’s report to Congress in June, you’ll know that the administration is claiming that our military actions in Libya are not covered under the War Powers Resolution which would require them to be terminated after 60 days. To get around this window, there must be […]
What has Al Franken done for me lately, Part 1
In February of this year, the Senate Judiciary Committee voted to form a new sub-committee on Privacy, Technology, and the Law. They chose my favorite Senator, Al Franken to chair the new group. After I heard about this new committee’s formation back in February (feb 14), they kinda went radio silent for a few months, […]
2011 US Information Security Related Measures
So far, in the first 6 months of 2011, there have been 9 different Information Security related proposals put forward by different Senators that would create new laws or reform existing ones. February 20 2011 – Rep. Rush (D-Ill) reintroduces BEST PRACTICES Act April 7 – SEC Regulation S-P mandates that financial firms safeguard confidential […]
Senator Leahy Introduces the Personal Data Privacy and Security Act of 2011
According to Senator Leahy’s website, the Personal Data Privacy and Security Act would: •Increasing criminal penalties for identity theft involving electronic personal data and making it a crime to intentionally or willfully conceal a security breach involving personal data; •Giving individuals access to, and the opportunity to correct, any personal information held by commercial data […]
Market Forces in Identity Theft
There can be real economic damages to an individual who is the victim of identity theft. The FTC has ruled that it is the individual’s responsibility to check their credit card statements for unauthorized statements.If a victim of credit card theft, for example, notifies the credit card company within 60 days of receipt of the […]
“Do-not-track Online Act of 2011â€
This month, Senate Commerce Chairman Jay Rockefeller (D-W.Va.) introduced the “Do-not-track Online Act of 2011â€. Some interesting highlights from the proposed bill: there would be a fine of up to $16,000 per day that you are in violation with a maximum of $15,000,000 in civil damages available for all civil actions under the bill.The $16,000 […]
Sony PSN Continued
I was curious to see whether the Sony figure of $150 million included any fines or other breakdown on how the financial impack might play out. Sony’s financial forecast revision statement to their investors appears to not address fines from Visa or others. They also, rightly, do not speculate on what a settlement package might […]
Sony PSN Breach
One of the reasons I decided to start an Information Security blog is that after researching some of the issues around the Sony PlayStation Network Breach that occurred in April I was left with more questions than answers.One of the things that I’ve noted is that there are very few blogs out there that deal […]
IANAL, But.
The word most written on the Internet after the acronym, IANAL is “But.” The acronym, if you’re not familiar, stands for “I am not a lawyer.” The author of the article, post, or blog will then go on to elaborate on a legal concept or issue. The greatness of the Internet is that it allows […]
