Culture Eats Cybersecurity For Breakfast

Eggo Waffles weren’t always called Eggo Waffles. In the 1950s, in the boom that followed World War II, Americans began a love affair with frozen foods. Frank Dorsa and his three brothers in San Jose California had been running a highly popular mayonnaise business and had expanded into powdered waffle mix, but demand for their […]
Unsolicited Advice For Solicitors: Part Deux – An Unexpected Calendar Entry

I got a calendar invite from a vendor this week. Several of my colleagues were included, but not ones that I would normally meet with. I had never met this vendor before. I had never exchanged emails with this salesperson. I checked with my colleagues and none of them had ever had a conversation with this individual either. As I […]
What Toys R Us Taught Me About Growing Up
When I was in high school, I got a job working at Toys R Us. It was one of the best jobs I ever had, and to this day I still think about all of the lessons I learned about service to others, responsibility, and integrity. My secret ambition was to be able to wear […]
The Funny Thing About Blind Spots

When I was in college, I got a job one summer at a comedy club. It wasn’t as glamorous as it sounds. I didn’t get to meet any comedians. My job was essentially a telemarketer. I would call people who had attended previous shows and tell them they had won free tickets to see the […]
The Best Job I Ever Had

“Security is mostly a superstition. It does not exist in nature, nor do the children of men as a whole experience it. Avoiding danger is no safer in the long run than outright exposure. Life is either a daring adventure, or nothing.†-Hellen Keller In honor of Labor Day, I’ve been reflecting on my career […]
Cybersecurity New Years Resolution
I don’t normally make New Year’s resolutions. But when I do, I start them in March. As you may have noticed, I decided to start blogging again. I published a book last year on cybersecurity for the layperson (managers, salespeople, executives) and I knew I wanted to begin writing a sequel. I didn’t have a theme […]
Cybersecurity Training Scars

There’s an old story in law enforcement circles that comes from the era of revolvers. During practice, officers would dump their spent brass cartridges into their hand after shooting a round rather than letting the brass fall to the floor where other people might slip and fall on it. Officers would then take the time to put […]
An OSI Model for Security Awareness

There are two parts of every great performance: the outer game and the inner game. Most books on coaching focus on the outer game. The outer game is what happens on the field. What sport are you playing? What plays are happening? What techniques are you using to hold or hit the ball? How do […]
The Nine Habits of Highly Effective Cybersecurity People

I was interviewing a manager recently about his department’s cybersecurity practices when I asked him whether they lock their paper records up at night. He said yes, they keep their files locked at all times, not just at night. I pointed to the filing cabinet in his office, where they key was still sticking out […]
Cybersecurity Role Models

Every time I interview a candidate, I ask, “Who is your role model in cybersecurity?†Some candidates name famous hackers, like Kevin Mitnick. Others choose well-known journalists like Brian Krebs or a prolific writers like Bruce Schnier. One candidate said their role model was Neo from the Matrix movies. There isn’t any right answer to this […]
The Next Generation of Security Professionals

Yes…that’s me and my wife, hanging out with Jeordi LaForge (LeVar Burton), Dr. Beverly Crusher (Gates McFadden), and Mr. Data (Brent Spiner). Trek yourself before you wreck yourself. In The War of Art, Steven Pressfield says that the difference between an amateur and a professional is that the professional has a plan. According to CSO […]
Unsolicited Advice For Solicitors
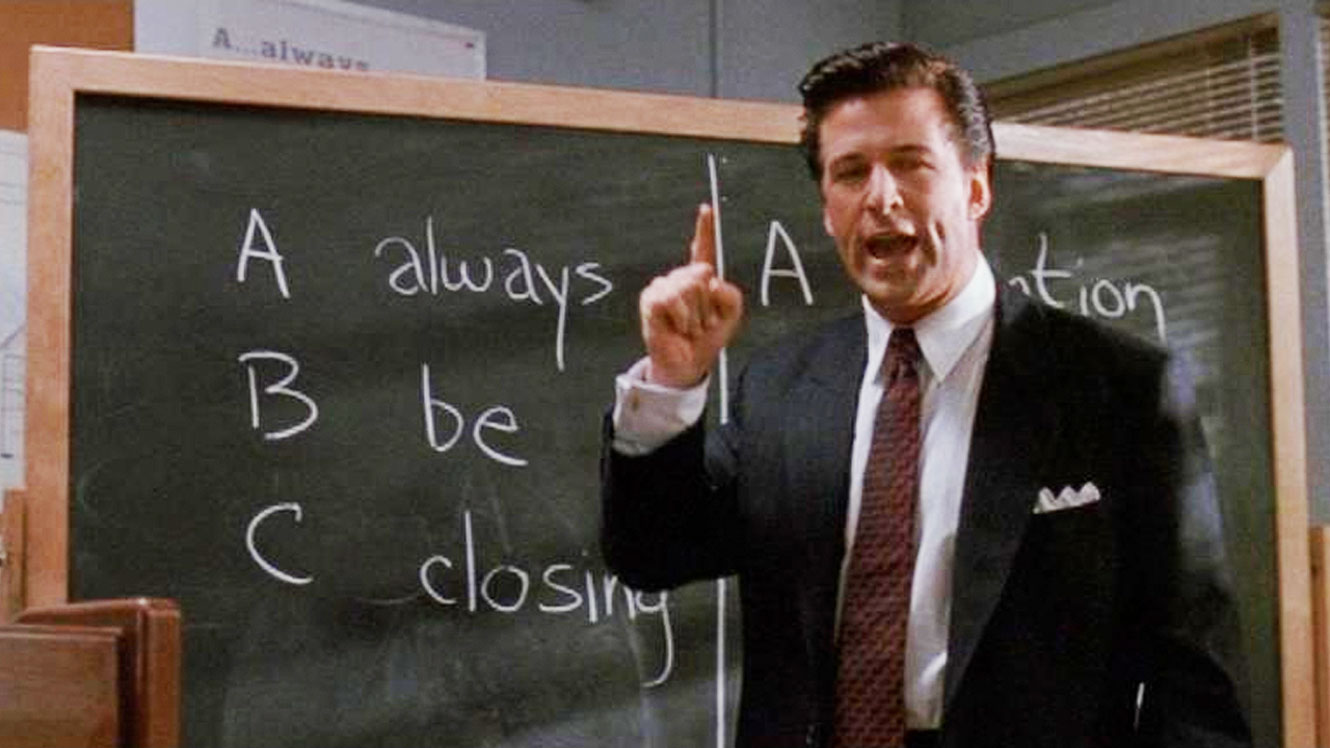
“These are the new leads. These are the Glengarry leads. And to you they’re gold, and you don’t get them. Why? Because to give them to you is just throwing them away. They’re for closers.†–Glengarry Glen Ross This past week I got around 70 cold calls or emails from vendors I’ve never worked with […]
Cybersecurity’s Happy Gilmore Problem
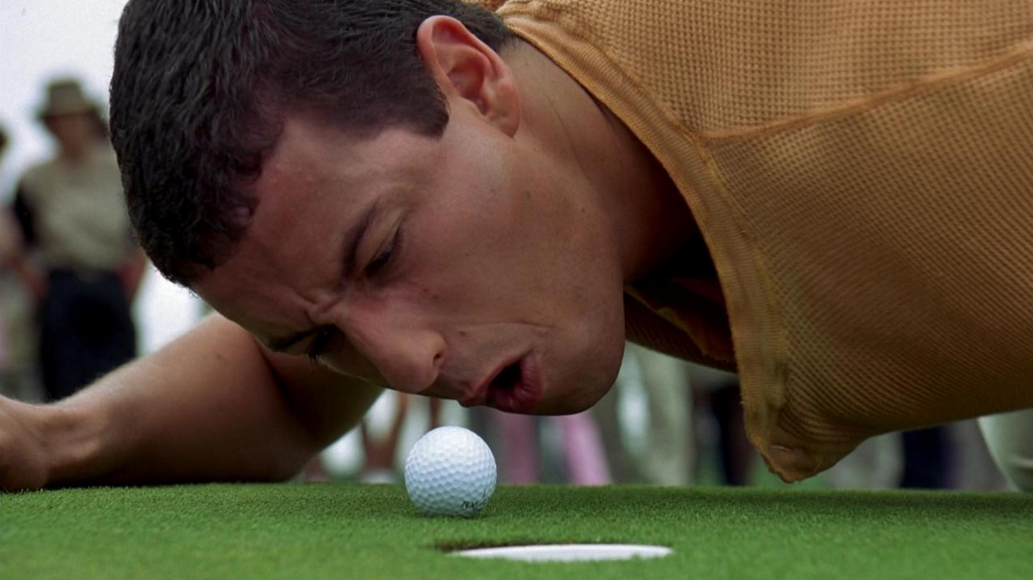
People, processes, and technology are the three parts of every security program. Sometimes, people make the mistake of believing that technology is the biggest or most important part. It isn’t. It might be the easiest part, since you can make quick changes to technology and buy new things to instantly improve it. But the biggest […]
Between The Keyboard And The Chair

I have a lot of respect for people who work at a help desk. When I was right out of college, I got a job at a call center. I had to take an average of one call every 4 minutes. That means I talked to 120 people every day on average, and a lot […]
The Strongest Element

In Cybersecurity we refer to employees as the Human Element. We generally call the Human Element the weakest link in Cybersecurity. It’s easy to see the logic in this, but unfortunately for many of us, this is wrong. Humans are the Strongest Element in Cybersecurity. Sure, humans are the ones that make the mistakes. They […]
Embracing Wellness in CyberSecurity

CyberSecurity is a life skill.
Discussion Draft of the SAFE Data Act introduced by Representative Mary Bono Mack (R-CA)
On June 13th, Congresswoman Mary Bono Mack released a discussion draft of what she calls the SAFE Data Act. Here’s the marketing release if you’d prefer to read the cliff notes. Since it’s a discussion draft, let’s discuss! Actually, I think this could be a good bill to eliminate a lot of the confusion about […]
2011 US Information Security Related Measures
So far, in the first 6 months of 2011, there have been 9 different Information Security related proposals put forward by different Senators that would create new laws or reform existing ones. February 20 2011 – Rep. Rush (D-Ill) reintroduces BEST PRACTICES Act April 7 – SEC Regulation S-P mandates that financial firms safeguard confidential […]
IANAL, But.
The word most written on the Internet after the acronym, IANAL is “But.” The acronym, if you’re not familiar, stands for “I am not a lawyer.” The author of the article, post, or blog will then go on to elaborate on a legal concept or issue. The greatness of the Internet is that it allows […]
